Security Risks of Third-Party Facebook Follower Services: Data Harvesting, Malware, and Account Breaches

Data harvesting, malware infections, and account breaches are just a few of the dangers lurking behind these shortcuts. The desire to grow social media presence quickly has led many to consider third-party follower services, even when looking for top sites to buy Facebook followers. These platforms promise rapid increases in likes, follows, and engagement. While the allure is strong, using such services carries serious security risks. Understanding these risks is critical for anyone seeking to expand their online influence without compromising security. This article explores the technical, operational, and security concerns associated with third-party follower services.
The Appeal of Third-Party Services
Third-party follower services promise fast results. For businesses, influencers, or individuals, instant growth can seem enticing. The idea of appearing popular overnight can help with social proof and brand perception. However, these services often operate outside the terms of use of platforms. They may offer real or fake followers, automated likes, or engagement pods. While the numbers rise quickly, the underlying security risks are often ignored or underestimated.
Privacy Concerns and Data Harvesting
One of the primary dangers of third-party follower services is data harvesting. To use these services, users often provide login credentials or grant extensive permissions. This access allows the service to collect sensitive information, including email addresses, contact lists, and private messages. Malicious actors may sell this data or use it for phishing campaigns. Even reputable services can inadvertently expose user data. The consequences of data harvesting extend beyond social media, affecting personal and professional privacy.
Account Breaches and Unauthorized Access
Providing credentials to third-party platforms increases the risk of account breaches. Malicious services can hijack accounts, post content without permission, or lock users out entirely. Even accounts used for business purposes may be affected, leading to reputational damage and lost connections. Platforms like Facebook, Instagram, and Twitter actively monitor suspicious activity and may flag or suspend accounts. Breaches not only threaten personal security but also jeopardize professional and commercial credibility.
Malware and Device Compromise
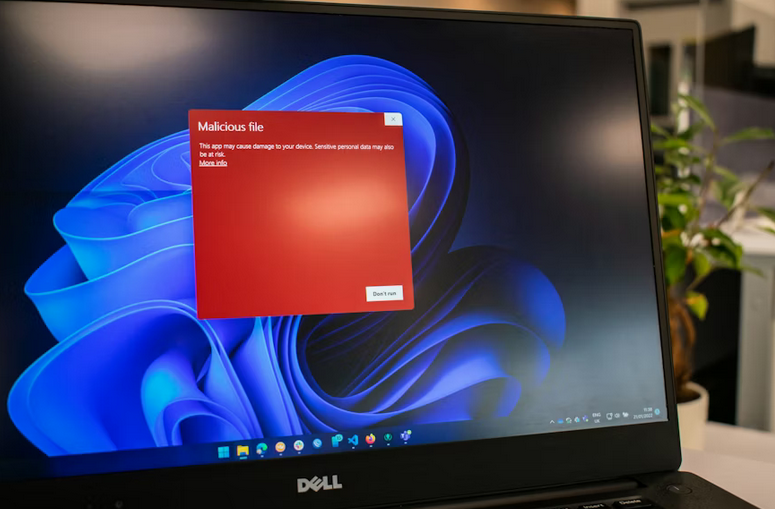
Some follower services carry malware or spyware. Malicious software can be embedded in apps, websites, or downloadable tools. Once installed, malware can track keystrokes, capture login information, or gain remote access to devices. Infected devices are vulnerable to further attacks, including ransomware or unauthorized transactions. Users seeking to gain followers may unknowingly compromise their entire digital environment. Malware risks are a serious concern that cannot be overlooked when using third-party services.
Algorithmic Detection and Platform Penalties
Social media platforms use algorithms to detect unnatural activity. Sudden spikes in followers, automated engagement, or suspicious logins are flagged as potential violations. Accounts tied to third-party services may face restrictions, temporary locks, or permanent bans. Using these services may appear safe initially, but detection can result in serious penalties. The risk of losing an established following far outweighs the short-term benefits offered by third-party platforms.
Financial and Operational Risks
Third-party follower services can also pose financial risks. Some services charge recurring fees, often without providing promised results. Failed services or compromised accounts may …
