Security Risks of Third-Party Facebook Follower Services: Data Harvesting, Malware, and Account Breaches

Data harvesting, malware infections, and account breaches are just a few of the dangers lurking behind these shortcuts. The desire to grow social media presence quickly has led many to consider third-party follower services, even when looking for top sites to buy Facebook followers. These platforms promise rapid increases in likes, follows, and engagement. While the allure is strong, using such services carries serious security risks. Understanding these risks is critical for anyone seeking to expand their online influence without compromising security. This article explores the technical, operational, and security concerns associated with third-party follower services.
The Appeal of Third-Party Services
Third-party follower services promise fast results. For businesses, influencers, or individuals, instant growth can seem enticing. The idea of appearing popular overnight can help with social proof and brand perception. However, these services often operate outside the terms of use of platforms. They may offer real or fake followers, automated likes, or engagement pods. While the numbers rise quickly, the underlying security risks are often ignored or underestimated.
Privacy Concerns and Data Harvesting
One of the primary dangers of third-party follower services is data harvesting. To use these services, users often provide login credentials or grant extensive permissions. This access allows the service to collect sensitive information, including email addresses, contact lists, and private messages. Malicious actors may sell this data or use it for phishing campaigns. Even reputable services can inadvertently expose user data. The consequences of data harvesting extend beyond social media, affecting personal and professional privacy.
Account Breaches and Unauthorized Access
Providing credentials to third-party platforms increases the risk of account breaches. Malicious services can hijack accounts, post content without permission, or lock users out entirely. Even accounts used for business purposes may be affected, leading to reputational damage and lost connections. Platforms like Facebook, Instagram, and Twitter actively monitor suspicious activity and may flag or suspend accounts. Breaches not only threaten personal security but also jeopardize professional and commercial credibility.
Malware and Device Compromise
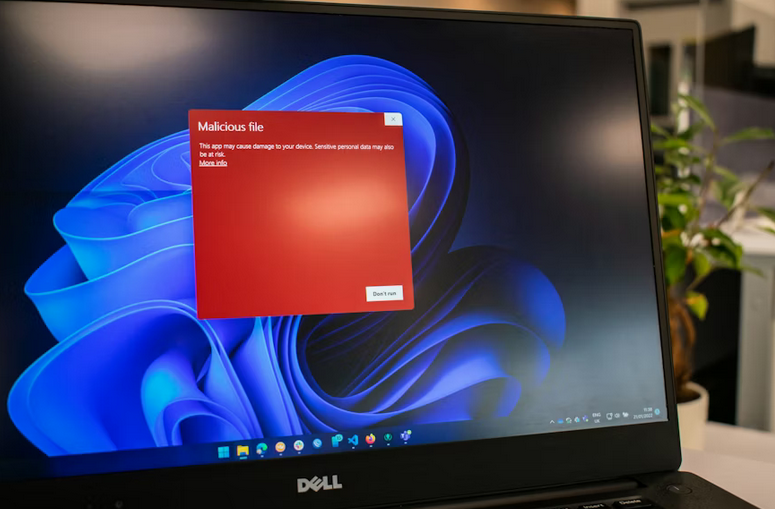
Some follower services carry malware or spyware. Malicious software can be embedded in apps, websites, or downloadable tools. Once installed, malware can track keystrokes, capture login information, or gain remote access to devices. Infected devices are vulnerable to further attacks, including ransomware or unauthorized transactions. Users seeking to gain followers may unknowingly compromise their entire digital environment. Malware risks are a serious concern that cannot be overlooked when using third-party services.
Algorithmic Detection and Platform Penalties
Social media platforms use algorithms to detect unnatural activity. Sudden spikes in followers, automated engagement, or suspicious logins are flagged as potential violations. Accounts tied to third-party services may face restrictions, temporary locks, or permanent bans. Using these services may appear safe initially, but detection can result in serious penalties. The risk of losing an established following far outweighs the short-term benefits offered by third-party platforms.
Financial and Operational Risks
Third-party follower services can also pose financial risks. Some services charge recurring fees, often without providing promised results. Failed services or compromised accounts may …











 Black box testing is like solving a puzzle without any hints or clues. The tester has no prior knowledge about the system being tested and must rely solely on their skills and expertise to uncover vulnerabilities. This type of testing simulates an external hacker trying to gain unauthorized access. On the other hand, white box testing provides testers with full access and knowledge of the system’s inner workings.
Black box testing is like solving a puzzle without any hints or clues. The tester has no prior knowledge about the system being tested and must rely solely on their skills and expertise to uncover vulnerabilities. This type of testing simulates an external hacker trying to gain unauthorized access. On the other hand, white box testing provides testers with full access and knowledge of the system’s inner workings.




 If you start receiving emails or messages …
If you start receiving emails or messages …
 A comfortable gaming chair is essential for any gamer. Not only does it give you a better gaming experience, but it also helps protect your back from the strain of long hours of playing. Invest in a gaming chair with adjustable arms and lumbar support so that you can adjust it to fit your body type perfectly.
A comfortable gaming chair is essential for any gamer. Not only does it give you a better gaming experience, but it also helps protect your back from the strain of long hours of playing. Invest in a gaming chair with adjustable arms and lumbar support so that you can adjust it to fit your body type perfectly. A quality headset and microphone are essential for gaming. Invest in a good pair that is comfortable, lightweight, and has noise cancellation capabilities to concentrate on the game without any distracting background noise. Look for one with clear sound quality so your teammates can hear you clearly during online gaming sessions.
A quality headset and microphone are essential for gaming. Invest in a good pair that is comfortable, lightweight, and has noise cancellation capabilities to concentrate on the game without any distracting background noise. Look for one with clear sound quality so your teammates can hear you clearly during online gaming sessions. A good hard drive is essential for gamers who need to store large gaming files. Invest in one with plenty of space and the latest technologies, such as SATA, USB 3.0, or Thunderbolt, so you can transfer data quickly and easily. Also, look for one that has an external power source so you can take it with you when needed.
A good hard drive is essential for gamers who need to store large gaming files. Invest in one with plenty of space and the latest technologies, such as SATA, USB 3.0, or Thunderbolt, so you can transfer data quickly and easily. Also, look for one that has an external power source so you can take it with you when needed.
 In addition to 24-track recording, the 1970s also saw the development of hi-fi cassette decks. This technology allowed for high-quality audio playback, perfect for listening to rock music.
In addition to 24-track recording, the 1970s also saw the development of hi-fi cassette decks. This technology allowed for high-quality audio playback, perfect for listening to rock music. The most advanced technology innovation of the 1970s for rock music was the large-scale live sound system. This technology allowed bands to create an epic, stadium-sized sound in any venue. The live sound system consisted of multiple loudspeakers and amplifiers, creating a substantial sonic power wall. This technology helped redefine the concert experience and make rock concerts into spectacles.
The most advanced technology innovation of the 1970s for rock music was the large-scale live sound system. This technology allowed bands to create an epic, stadium-sized sound in any venue. The live sound system consisted of multiple loudspeakers and amplifiers, creating a substantial sonic power wall. This technology helped redefine the concert experience and make rock concerts into spectacles.

 The most expensive CPU and GPU are because they’re what your computer needs to execute instructions. The more powerful the CPU is, the more it will cost. The graphics card is used to play video games. The graphics card will be more powerful the more gigabytes that you have. However, the card will cost more if you have more gigabytes.
The most expensive CPU and GPU are because they’re what your computer needs to execute instructions. The more powerful the CPU is, the more it will cost. The graphics card is used to play video games. The graphics card will be more powerful the more gigabytes that you have. However, the card will cost more if you have more gigabytes.





 The settings/preferences section in Chrome includes a couple of things that could make it quicker. Regrettably, a few of Chrome’s default options appear to slow down Chrome. To get there, open your Chrome browser. In the address bar, type “about:configurations” or”chrome://preferences”. Scroll to the bottom of the page and click on “Show advanced settings.” This will expand the web-page giving you access to settings.
The settings/preferences section in Chrome includes a couple of things that could make it quicker. Regrettably, a few of Chrome’s default options appear to slow down Chrome. To get there, open your Chrome browser. In the address bar, type “about:configurations” or”chrome://preferences”. Scroll to the bottom of the page and click on “Show advanced settings.” This will expand the web-page giving you access to settings.




 The TrailGuru program is based on Google Maps, and the listed trails are visible on Google Earth. TrailGuru monitors altitude and speed, but not elsewhere. The site is much easier to use than several other action logs, with fewer data. You can add activities manually, without the need for a map. All actions depend on the results obtained, which helps members to stay motivated.
The TrailGuru program is based on Google Maps, and the listed trails are visible on Google Earth. TrailGuru monitors altitude and speed, but not elsewhere. The site is much easier to use than several other action logs, with fewer data. You can add activities manually, without the need for a map. All actions depend on the results obtained, which helps members to stay motivated. 



 Securing your
Securing your